Overview
This guide walks through creating a Windows provisioning package (.PPKG) using Windows Configuration Designer (WCD). The package can be used during imaging or first boot (OOBE) to automatically configure and enroll devices into Microsoft Entra ID and Intune.
Applies To
- Windows 10 and Windows 11
- Microsoft Entra ID (Azure AD)
- Microsoft Intune Enrollment
- Softdrive provisioning workflows
Prerequisites
- A Windows PC to build the provisioning package
- Entra ID join must be allowed by policy
- If using Intune, licensing and auto-enrollment must be enabled
Procedure
- Install Windows Configuration Designer
- Download the Windows ADK from: https://learn.microsoft.com/en-us/windows-hardware/get-started/adk-install
- Run adksetup.exe and install Windows Configuration Designer
- On the feature selection screen, select Windows Configuration Designer

- Create a new provisioning project
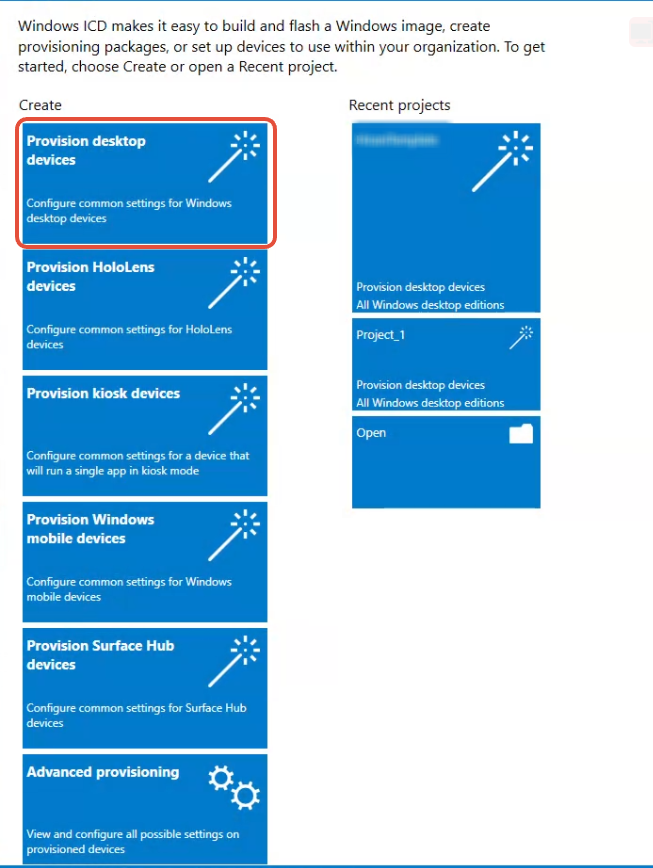
- Open Windows Configuration Designer
- Click "Provision desktop devices"
- Give your project a name (example: AutoJoin-Entra-Intune)
- Click Next until reaching the main editor
- Configure device settings

- Set the device name using a naming pattern
- Examples: COMP-%SERIAL%, VDI-%RAND:5%, SOFTDRIVE-%RAND:6%
- (Optional) Enter a product key if upgrading Windows edition
- Leave shared device mode set to No for most Softdrive environments
- Configure account management

- Enable Azure AD Join
- Sign in with an admin or enrollment account when prompted
- This allows automatic Entra ID join during OOBE
- Build the provisioning package
- Set Owner to IT Admin and version to 1.0
- Choose to sign the package or protect it with a password
- Click Build to generate the .ppkg file
- The package can be applied during imaging or first boot
Expected Result
Devices are automatically configured and joined to Microsoft Entra ID during deployment, with optional Intune enrollment applied without manual user intervention.
Troubleshooting
- Ensure ADK version matches the Windows version
- Verify Entra ID join policies allow device enrollment
- Confirm Intune auto-enrollment is enabled
- Validate credentials used during provisioning